
Premium Pentesting plan
Continuous Pentesting to build with confidence
Experience Pentesting augmented by technology that gets high-impact results.
Pentesting
Insightful security testing, all year round
Pentesting augmented by technology to discover high-impact vulnerabilities continuously.
Beyond traditional Pentest-as-a-service
Strike’s Continous Pentesting helps you secure your system without losing development momentum. Test regularly to identify zero-day vulnerabilities.

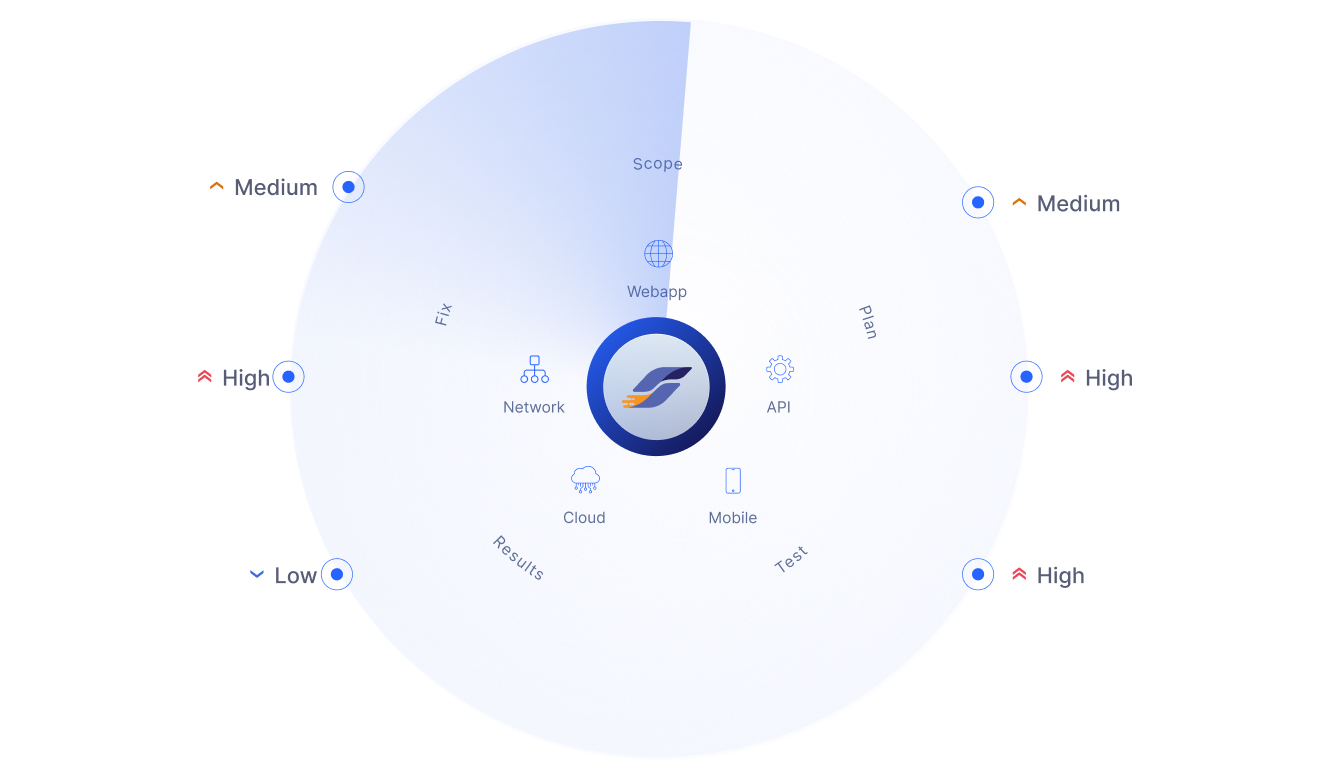
All types of pentests
Our ethical hackers can handle any time of pentest, including web apps, mobile apps, APIs, Cloud configurations and networks.
Flexibility
Adjust your scope on the go. Add more targets, attack vectors or change complete focus of the pentest as needed.
Transparency
Get a complete overview of everything that is happening on your pentest in a centralized place.
World-class ethical hackers
Work with the top 1% of the best ethical hackers out there. We call them Strikers, and they will discover vulnerabilities no one else can.
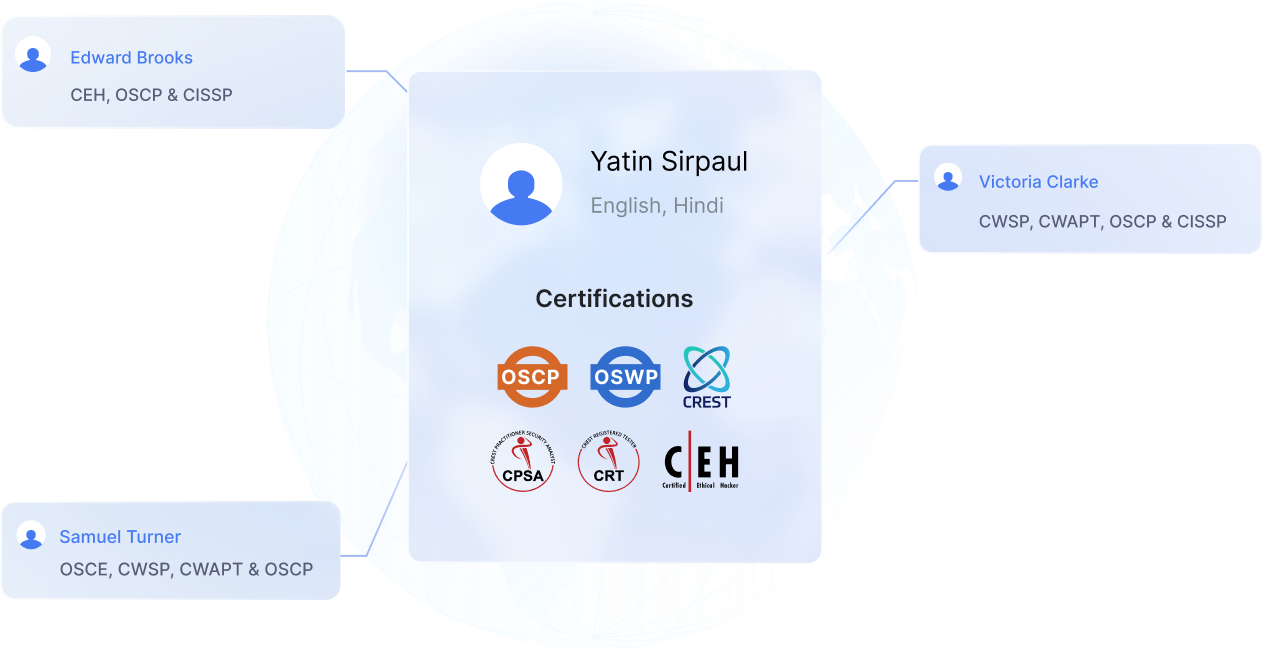

Hall of Fame
Strikers have discovered vulnerabilities so impactful that they are part of the cybersecurity Hall of Fame of Apple, Microsoft, Google, Amazon, and more.
Certifications
They have major credentials, such as OSEP, OSWE, OSCE, OSCP, OSWP, eWPTX, eMAPT, eCPPT, and more.
Professionalism
We work closely with Strikers to ensure the highest level of quality and professionalism while executing your pentest.
Strategic Partner
Discover unmatched customer service that is determined to help you accomplish your strategy and cybersecurity goals. Our Strategic Team will accompany you while defining your scope and will be available for weekly follow-ups.

Personalized onboarding
Dont, know exactly how many pentesting hours you will need? Our Strategic Team will work with you to determine the best scope.
Follow-ups
Get weekly follow-ups with the Strategic Team to better understand how your pentest is going.
Named CSM
A Customer Success Manager will be available just for you and will work to give you the best experience possible.
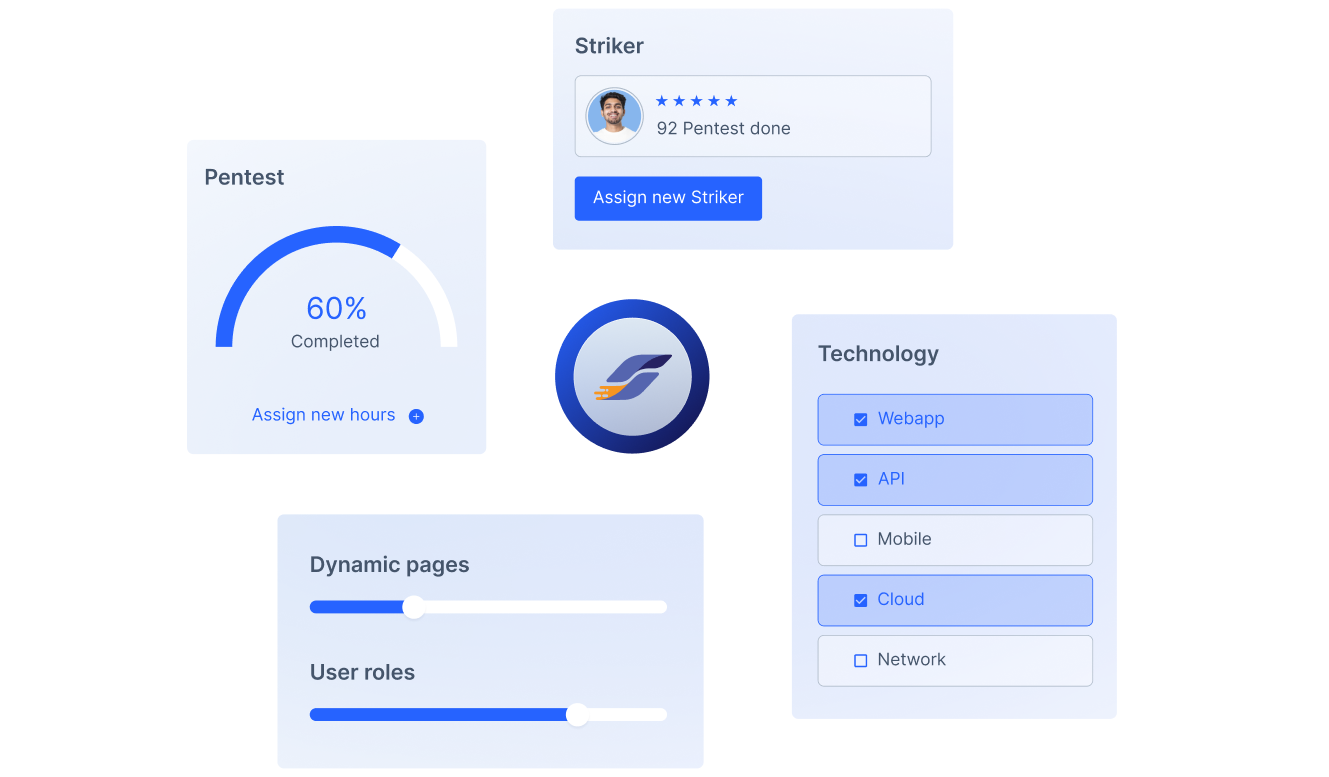
The most innovative pentesting platform
Strike does not hide anything about your pentest. Use our platform to see everything that is happening, from what is the Striker testing to what was already been found.
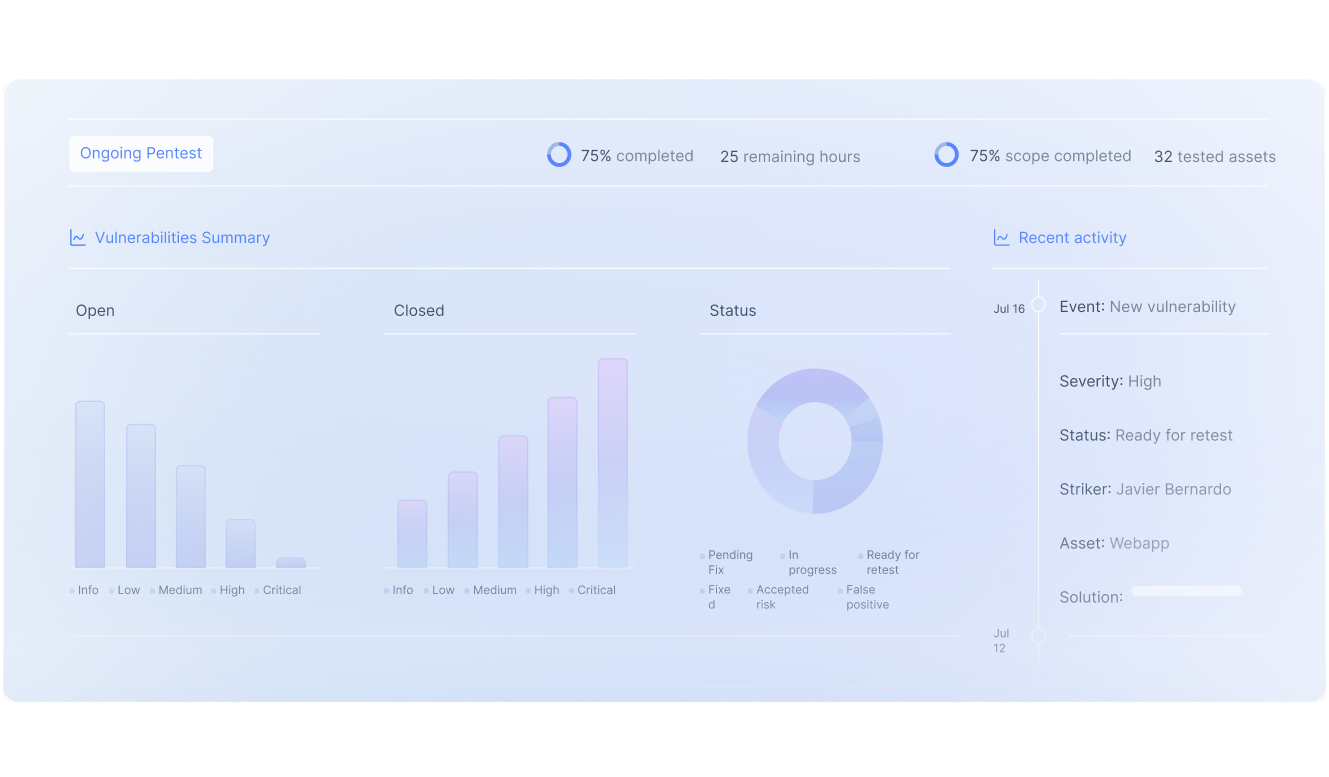

Vulnerability Manager
Get all your findings in a centralized place. Check details about every vulnerability even before the pentest ends.
Flexibility
Quick change of scope? Set new goals or targets on the go. The Striker will be notified and adjust their work to your needs.
Chat with your Striker
Learn about how each vulnerability has been found and how can be remediated by talking with your Strikers.
Pentesting, augmented
Augment the power of your pentest
Use Strike’s free security stack before, during, and after every pentest to get better results.
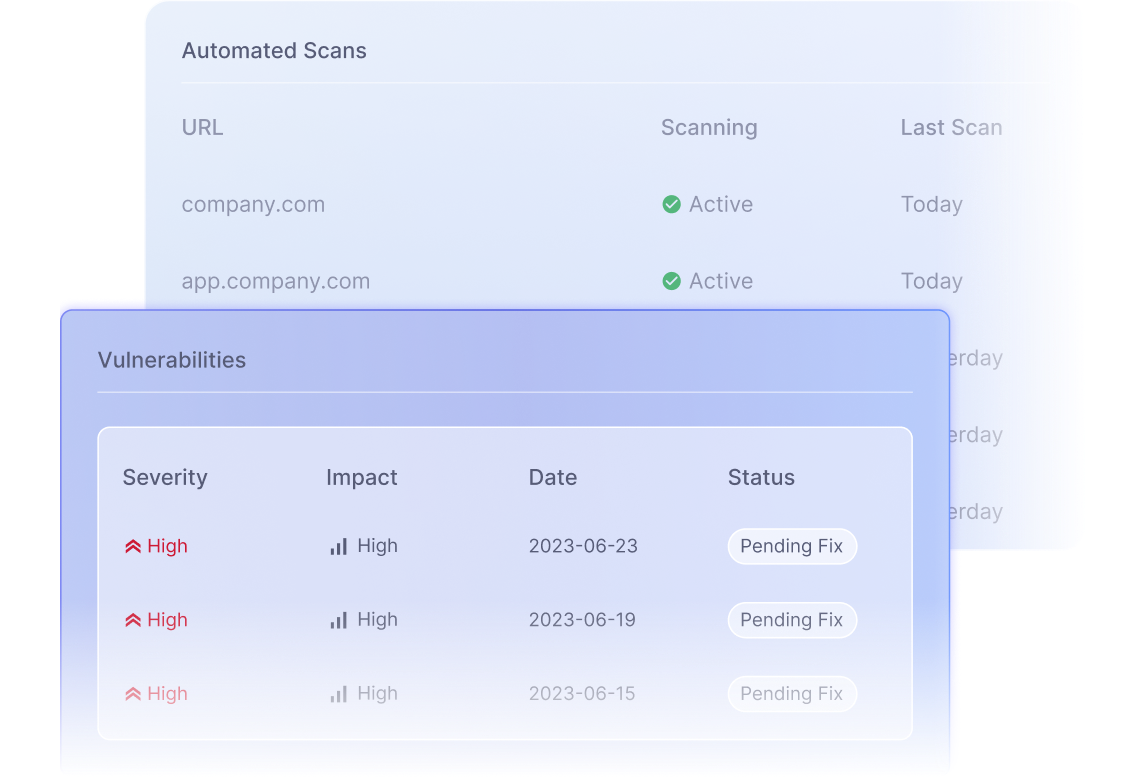
Automated Scans
Get your web-apps continuously scanned to find security vulnerabilities in development, staging and production environments. Strengthen your overall security over time.

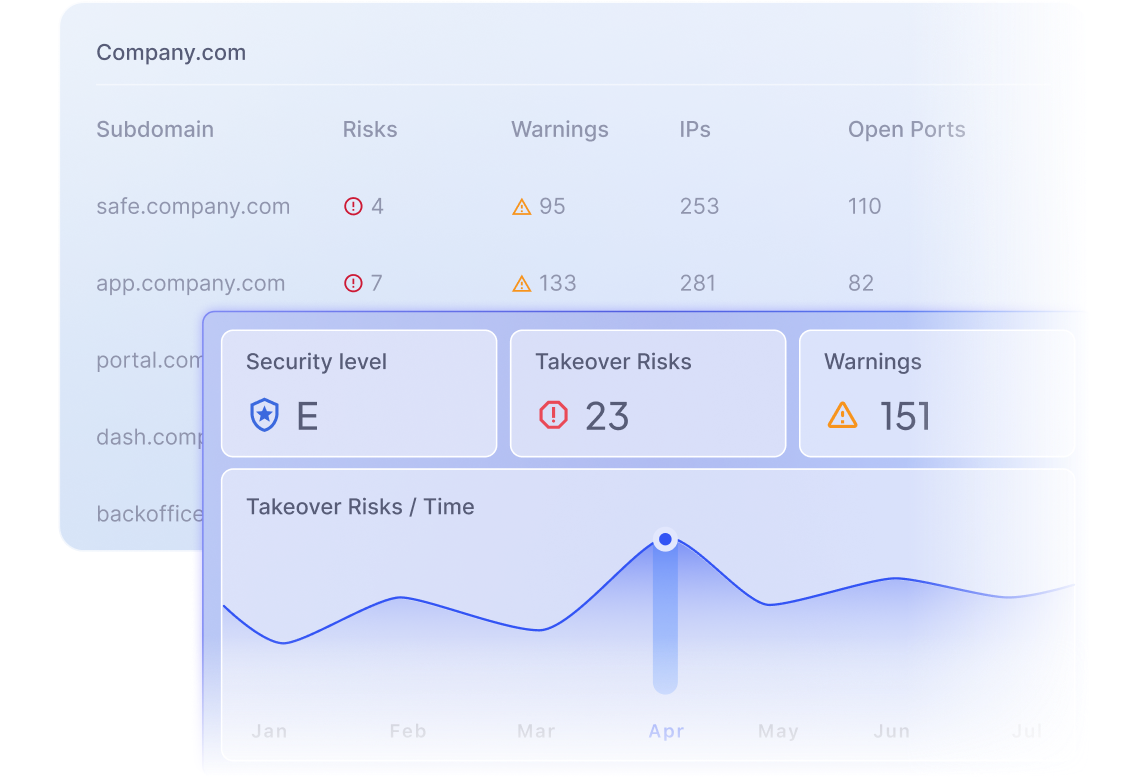
Attack Surface Monitoring
Maintain a continuous discovery and inventory of your organization’s assets. Prioritize your cybersecurity operations backed by data.

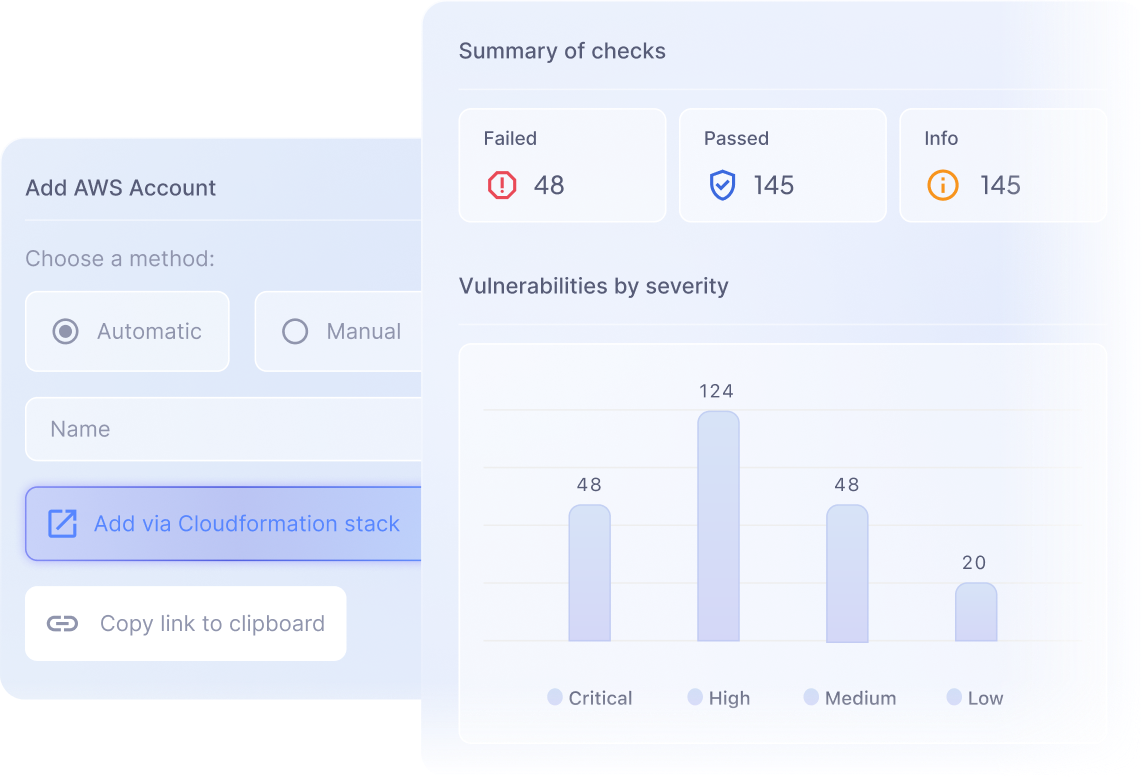
Cloud Security
Examine, analyze, and assess your cybersecurity in your cloud infrastructure. Identify all of your potential threats and obtain actionables, all in one place.

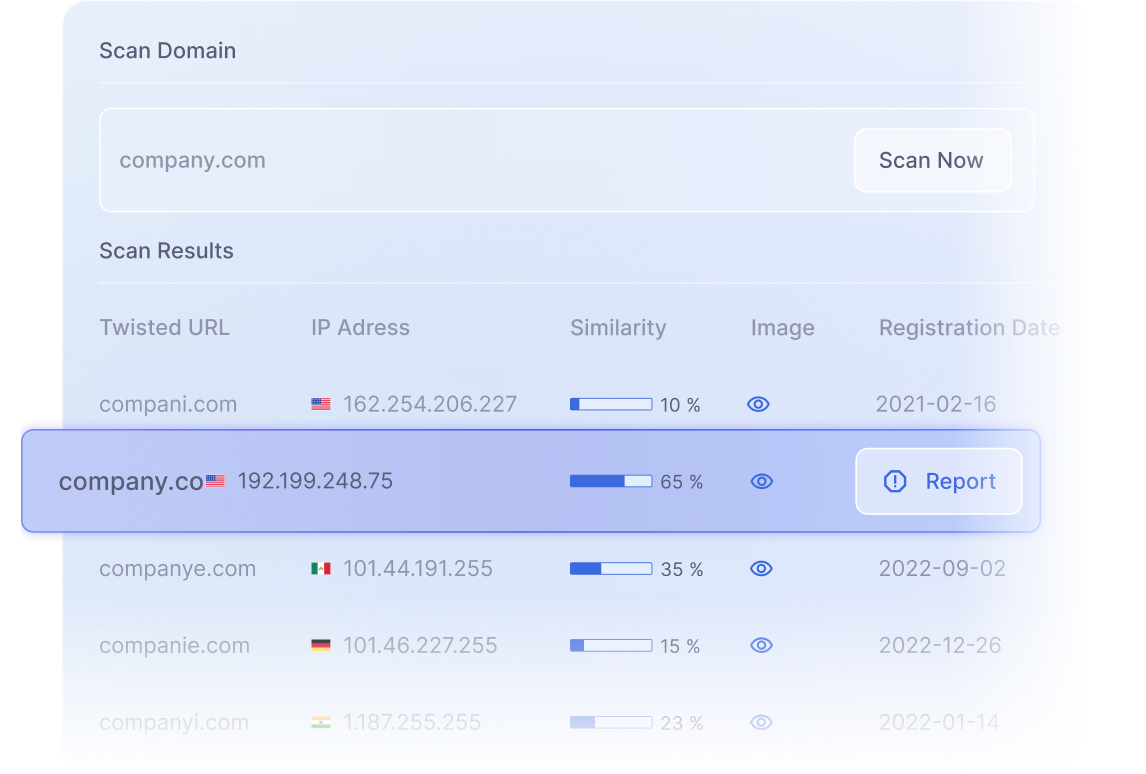
Phishing monitor
Scan over your domain and find which malicious URLs on the internet could potentially target your users for phishing attacks. See them all in one place.

Testimonials
“Working with Strike was an excellent experience for us. We were able to create our own pentests and change their scope each month. The Strikers are world-class professionals who provide us with relevant findings quickly and efficiently. Also, automated tools like Phishing Monitor are really interesting for our company, because they help us spot fake domains trying to impersonate PedidosYa.”


Eduardo Gimenez
Chief Information Security Officer
“Working with Strike is extremely important to us, especially because they deliver quality work over our products in a continuous way, and provide constant follow-up when it comes to managing the already found vulnerabilities. Moreover, they are constantly making improvements in their SaaS platform so we can have the best experience possible. In case we have a problem, they listen and help us. That’s invaluable.”


Ileana Barrionuevo
Sr. Application Security Engineer of SDI-RED Team
“For us at pier, security is the most important aspect, not only on the surface but throughout our entire product. When we reached out to Strike, we were looking for someone that could test & find vulnerabilities across our entire stack. We are very happy that we have found the right partner to achieve that, and we are looking forward to continuing this important work together.”


Andras Hejj
CEO & CTO
Start now
Get ready for your next pentest
Planning for a Pentest soon? Schedule a demo with our technical team or try our security stack for free
